I recently encountered an issue where we were experiencing connection issues to a new LDAPS server (LDAP over SSL). The connection all worked ok when using LDAP (the unsecured version of the Lightweight Directory Access Protocol). In this blog, I want to introduce Microsoft ldp.exe, which allows us to test the SSL connection with certificates.
Although Sage X3 has an inbuilt connection feature This tool proved useful in verifying the authentication as the issue, as opposed to the Sage X3 Syracuse component or its handling of certificates.
Where can you get ldp.exe
Ldp.exe is a tool from Microsoft that is provided with all Microsoft server operating systems and can be used as a stand-alone application.
To enable the tool, open server manager on your Microsoft Windows server.
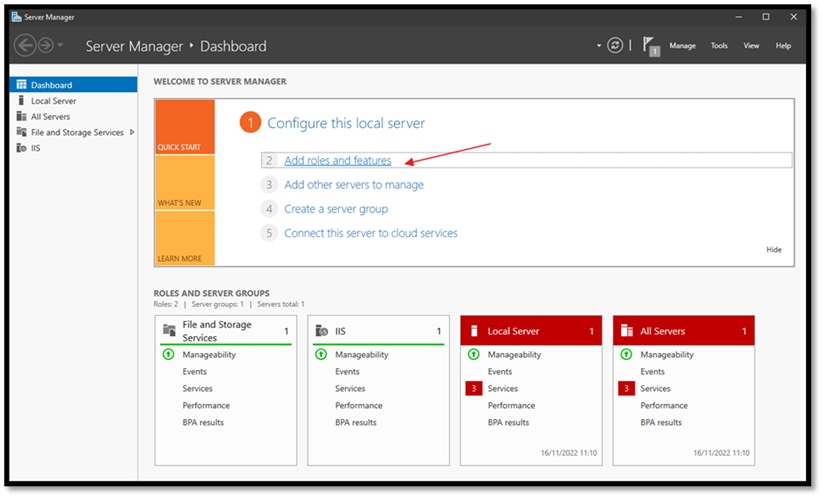
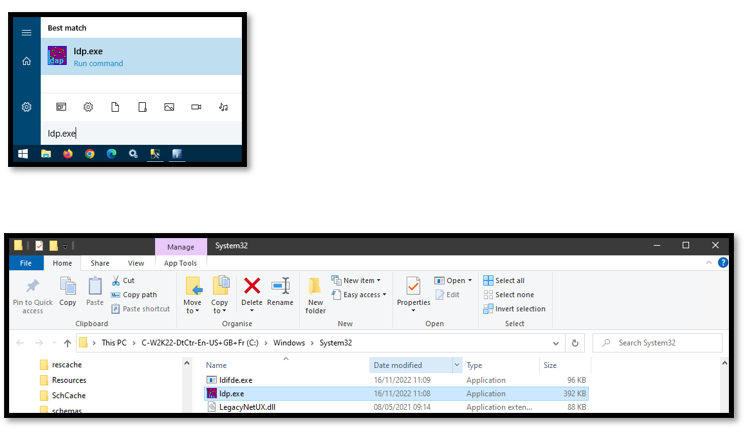
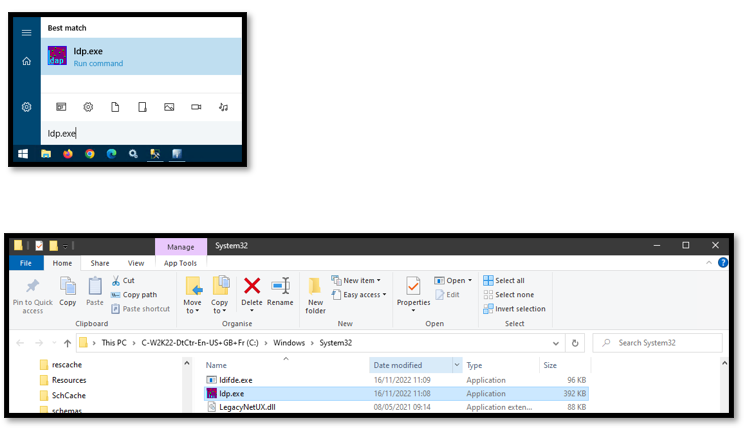
In features expand on remote server administration tools, role administration tools, and AD DS & AD LDS Tools select to install AD LDS Snap-ins & command line tools.
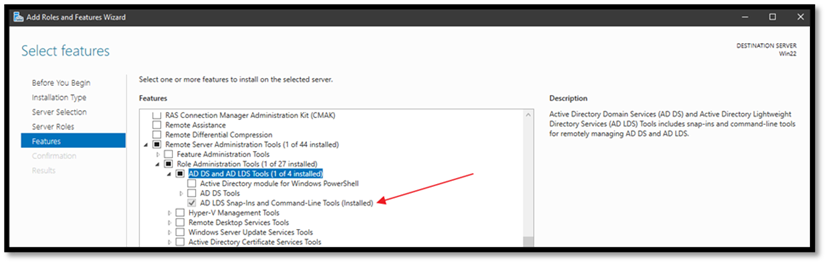
Ldp.exe will be available in the windows\system32 directory and can be accessed from the taskbar by typing ldp.exe
The Issue we faced
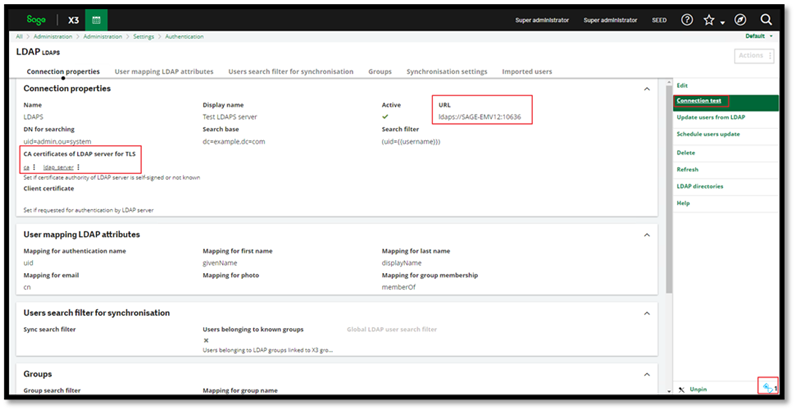
When configuring LDAPS authentication and using the ‘connection test function' there are a few hurdles that you could hit.
- Connectivity/Firewall related issues where LDAP ports are blocked on the Syracuse server, typically 389 for LDAP and 636 for Secure LDAPS.
- Secondly, connections are secured with certificates when using LDAPS. These could be invalid; the wrong certificates could have been supplied, or certificates in the incorrect formats
In our issue, the hourglass in Sage X3 would continuously load until we logged out of the session without any message of a connection test failure or success.
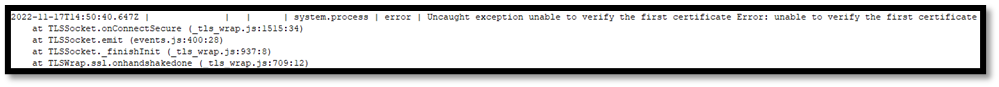
In the Syracuse logs, we could see the following error that pointed to an issue with the certificates.
system.process | error | Uncaught exception unable to verify the first certificate Error: unable to verify the first certificate
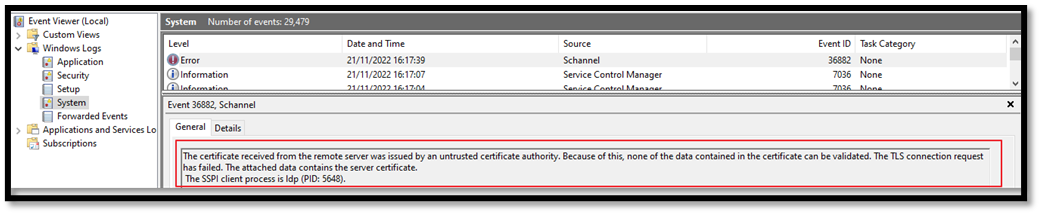
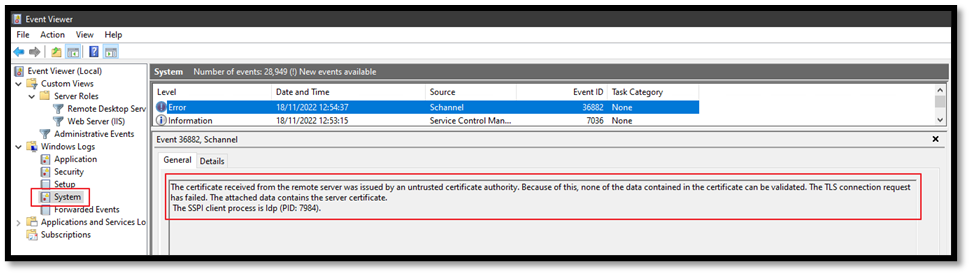
When I used the same certificates with ldp.exe to verify the connection I received the following error message generated by ldp.exe in the windows event viewer this contains more useful information which confirmed the results from Sage X3 that certificates were the likely cause of the connection failure.
Using ldp.exe to verify connectivity and authentication
Although the error message pointed to a certificate mismatch, I wanted a method to verify the authentication and connectivity to the LDAPS server before importing the new certificates into Syracuse. That’s where ldp.exe comes into play.
Ldp.exe has a graphical user interface it can be used to connect using the LDAP or LDAPS protocol using certificates and query information from your directory server. I will go through the steps I used to verify the connection but keep in mind that the tool does have advanced features and can let you perform additional tasks like
- Perform connect, bind, and search actions on your directory
- Modify, Add, or delete options against your directory
- View objects stored in your directory along with metadata and attributes.
Verify Connection using LDAP
In this instance, we could successfully verify our LDAP (unsecured) connection from Sage X3, but we wanted to test to make sure we get the same results using ldp.exe
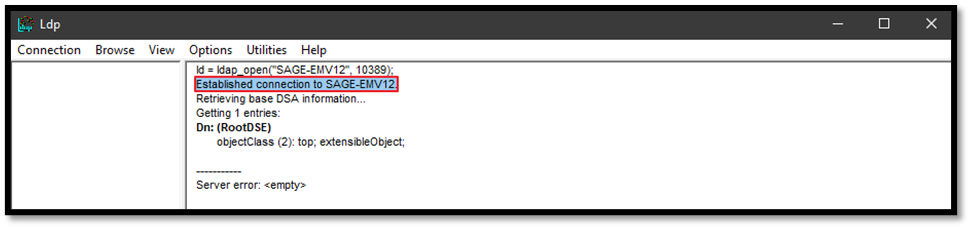
The first step is to populate the connection details. Connection > Connect The port is typically 389 in my case 10289
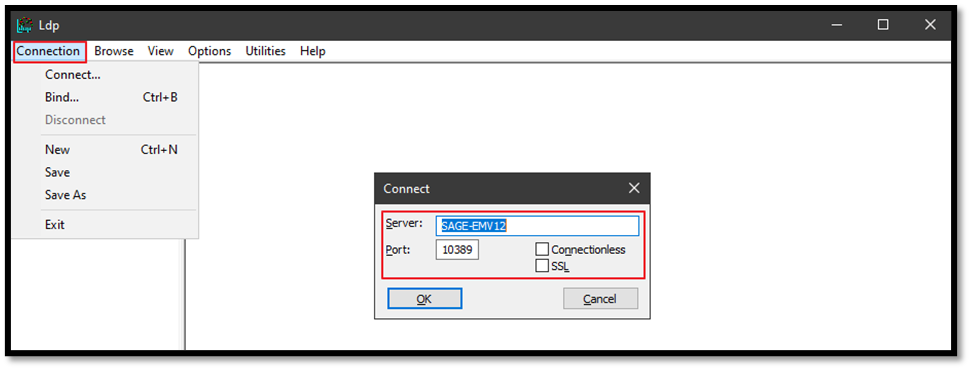
If the connection is successful in ldp.exe, we see the ‘established connection’ message. (the connection may be unsuccessful if name resolution is not working or ports are blocked)
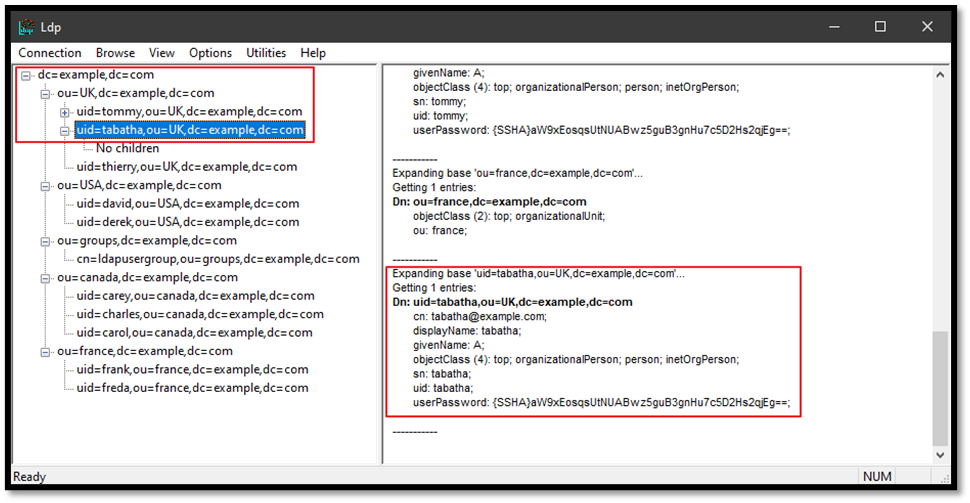
We can then further verify that the connection is authenticated by attempting to retrieve the directory tree information, (view > tree) populate the base DN & press ok.

The results will now show you detailed directory information.
Verify Connection using LDAPS with the new certificates
The LDAPS protocol uses certificates to authenticate and secure the connection between the directory server and the ldp.exe client. So, before we can test the LDAPS connection, we will need to import the certificates into the local windows certificate store on the machine where ldp.exe is installed.
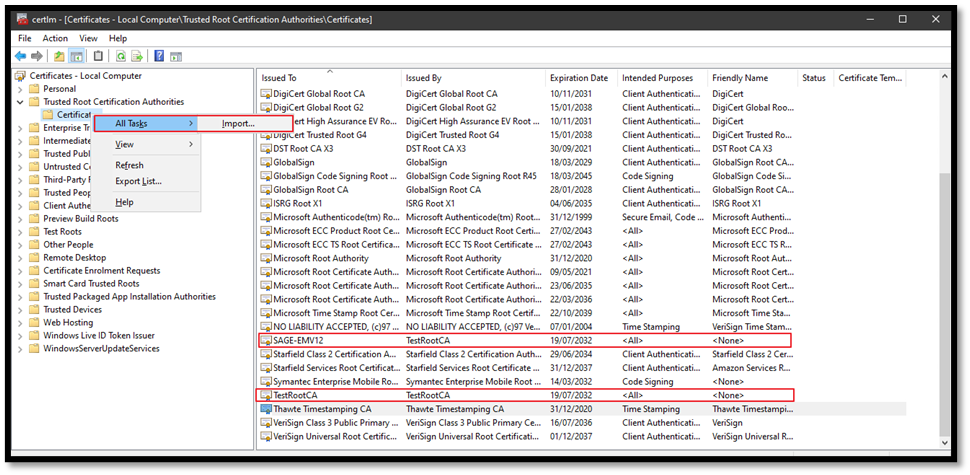
Importing certificates
To import certificates, click Start, and type certmgr.msc, which will open the certificate manager in the trusted root certification authorities and import the certificates provided by the directory server security team. Keep in mind that you will need to import the complete certificate chain.
Once the certificates are successfully imported, you can attempt to initiate a connection using Ldp.exe; the correct LDAPS port needs to be used, which is typically 636, in this case, 10636. You also need to ensure that SSL is selected so the certificates are used.
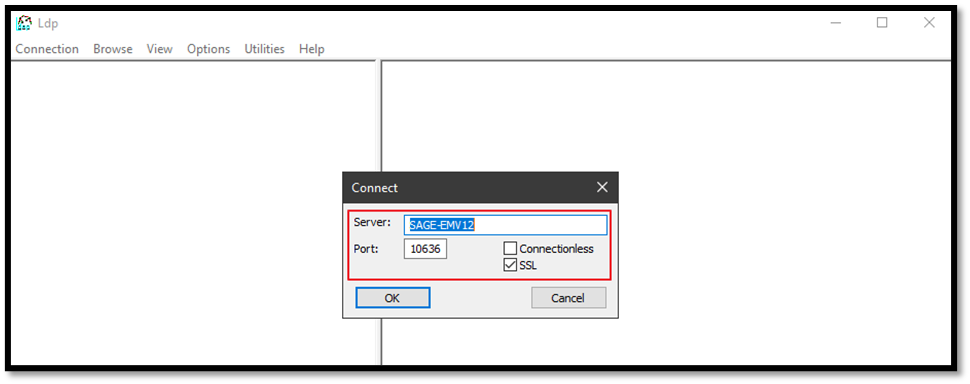
When the connection is successful using the LDAPS protocol, you will see the established connection message in the application.
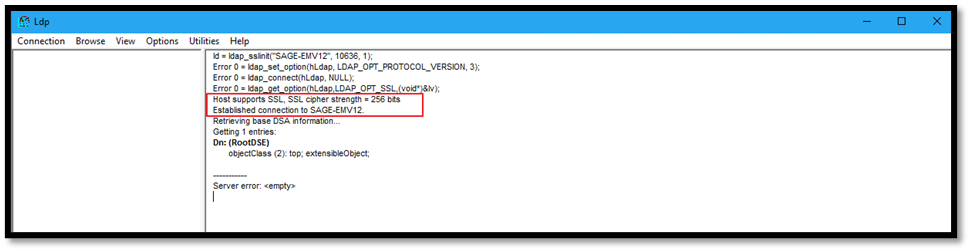
This test verified that the connection and certificate authentication is working, the certificates provided are correct, and we can now use the same certificates in Sage X3.
If the certificates are not installed correctly in the windows certificate store or the incorrect certificates have been supplied, and you attempt to initiate an LDAPS connection, you are likely to see the response Error <0x51>: Fail to connect to Server_name)
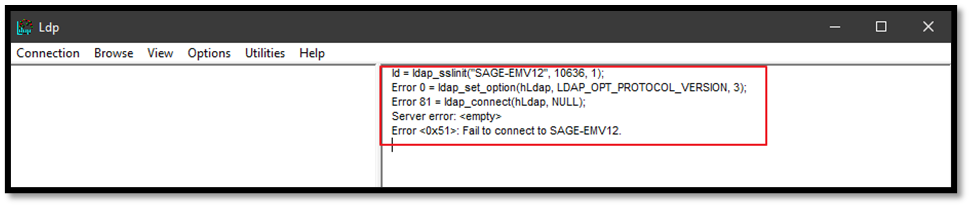
The failure to establish the connection will also be logged in the windows event viewer.
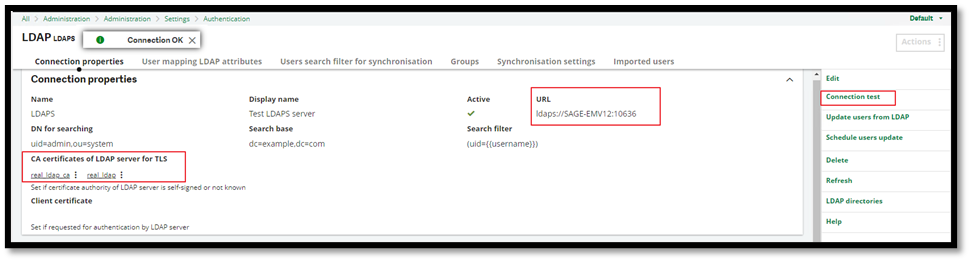
As the test showed that the connection was successful when testing with ldp.exe, we can now configure the Sage X3 connection to the LDAPS server.
- Import the certificates into Sage X3 CA certificates (Administration, certificates, certificates of certification authorities)

- In the LDAP server connection setting (Administration, Authentication, LDAP Servers), configure the connection making sure the correct URL & certificates are selected. The connection test will return the ‘Connection OK’ message
Hopefully, this blog has given you another way to test the connection to your LDAP server outside of X3, eliminating any issues stemming from the sage X3 Syracuse component and an introduction to the ldp.exe tool available from Microsoft.
Please note that the ldp.exe tool is not a Sage tool, so we cannot provide any support for this; however, a lot of helpful information is available online.

