This blog article will cover some tips on how you can secure your company data. Data security is an imperative function to any organistation. All data or information that relates to an identifiable individual that your business stores or handles needs to be properly protected. From financial information and payment details to agent’s, customers and suppliers contact information. All personal data must be protected by law.
- Data Security
Sage 200 Evolution stores all data in a Microsoft SQL Database. Each workstation with a Sage 200 installation needs to connect to a database using SQL Server Authentication where a connection username (usually sa) and a password is required. For additional security you may choose to enforce password policies as determined by your IT department as well as have an expiration on passwords to have them changed on a regular basis.
SQL login settings may be setup on Microsoft SQL Management Studio
SQL Instance | Security | Logins | sa |Right click and select Properties
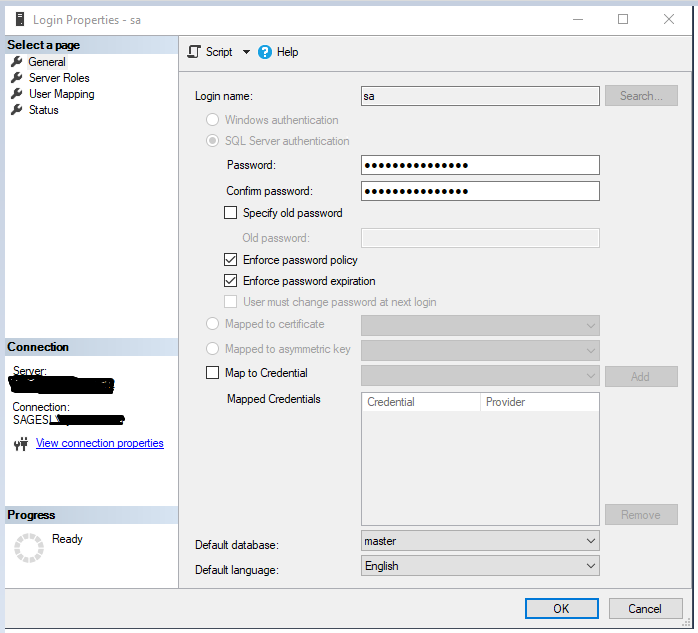
A dedicated server with advanced security is recommended to host the Microsoft SQL Database. It is also important that you have installed firewalls and opened the necessary firewall ports. It is also essential to manage the backups and ensure access is only given to security managers.
It is imperative to ensure that the connection set up for this database is secure by using strong passwords. No access should be given to users directly on the Microsoft SQL Database, this right should be reserved for System Administrators only.
2.Product Access
Sage 200 Evolution includes some access control features that allow one to work on an exception basis. One needs to set initial rules for what is supposed to happen most of the time. It is also necessary that you modify these rules for one or more agents or agent groups.
You set the initial default rules for agent access in the broadest possible terms. Once you do so, you can then modify the access rules at two levels:
You can set access rules per agent group. Any agent you link to the agent group then inherits the access settings for that group. If an agent belongs to more than one group, the system will merge the settings for these groups to determine the access.
You can set access rules per agent group. These are the strongest settings, and they override any other settings that may apply to the agent.
You can mix and match settings at the global level, agent group level, and agent level. The system will apply the most specific rules when they are present and move up a level when they are not.
To set up Access Control rules:
Navigate to Administrator | System Configuration | System Wizard
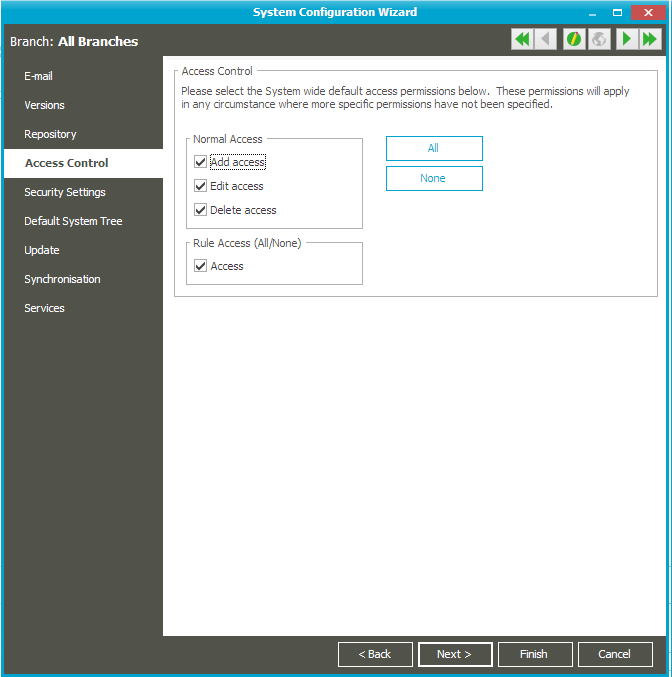
Add Access
- If you wish to allow most agents to create new master records in the modules in which they work, select this check box.
- If you prevent most agents from creating new master records, deselect this check box.
- In either case, you can modify this access rule per agent group or per agent.
Edit Access
- If you wish to allow most agents to edit existing master records in the modules in which they work, select this check box.
- If you prevent most agents from editing existing master records, deselect this check box.
- In either case, you can modify this access rule per agent group or per agent.
Rule Access
- In each module, you set rules. For example, you set whether an agent can sell an inventory item below cost. You set rules in the Access Permission tab of the agent or agent group.
- If you wish to turn on all rules by default, and then disable them where necessary, select this check box.
- If you wish to turn off all rules by default, and then enable them where necessary, deselect this check box.
3. Security Settings
You may setup your security settings by going to Administration | System Configuration | System Wizard
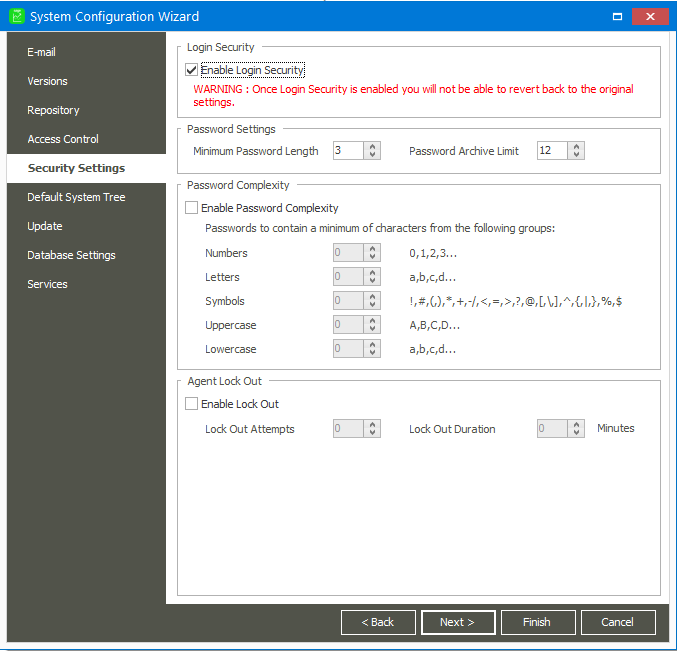
3.1 Login Security
The system contains two security models under which you can run. You choose a security model per company:
- Normal Security
- Login Security
Login Security provides enhanced security that protects passwords and agent login names. Without login security, you can still use passwords, however, the reduced security level allows agents to save password settings on a workstation. This, in turn, allows anyone to access the system from that workstation without knowing the password.
3.2 Password Settings
To enable login security:
- Select the Enable Login Security check box.
- In the Minimum Password length field, choose the lowest number of characters agents must enter when they create their passwords. Secure passwords need at least four characters. The more characters you use, the better.
- In the Password Archive Limit, specify how many older passwords the system should remember. Agents cannot use passwords that are in this archive. Once the system reaches this limit, the oldest password memory is erased each time an agent creates a new password.
Note: Once you enable login security, you cannot disable it.
Other changes that occur when you enable login security are:
- Whenever you log in, you must enter an agent name and a password. Without Login Security, you can save an agent name and/or a password on a workstation, thereby allowing access to unauthorised persons.
- The option to show password characters when you change passwords does not display.
3.3 Password Complexity
Password complexity settings allow for enhanced security that protects passwords by enforcing complex password combinations.
To enable password complexity
- Select the Enable Password Complexity check box.
- Specify the combination of characters listed.
- The combination listed will also determine the length of the password.
3.4 Agent Lock Out
This feature allows you to specify the number of login attempts allowed by an agent, as well as specify a duration whereby the system will automatically lock on behalf of the agent.
To enable agent lock out
- Select the Enable Lock Out check box.
- Specify the number of attempts allowed.
- Specify the time frame in case of no activity for the system to lock down.
There are other measure outside Sage 200 Evolution that could also assist in securing your data
- Regularly updating your Windows Firewall and anti-virus software, to prevent against hacking and virusses.
- Enforce security policies for all users working on or connecting to your main servers’.
- Password protect data files that are being compressed.
In conclusion, it is important to ensure that you have properly secured your company data as well as any stakeholder data that has been entrusted to the company. Not only will securing data prevent cyber criminals from accessing your sensitive data but this will also ensure that you are compliant with POPIA. Sage 200 Evolution provides some features to ensure that you have properly secured your data and restricted access. With cyber-attacks being on the rise it is imperative that you assert in protecting your company data.

